Risk assessment manual
Index
Definitions
ACL Anti-Corruption Law
AFB Applicant for Business
AML Anti-Money Laundering
AMLR Anti-Money Laundering Regulations
AMLCO Anti-Money Laundering Compliance Officer
MLRO Anti-Money Laundering Reporting Officer
DMLRO Deputy Money Laundering Reporting Officer
CDD Customer Due Diligence
CFT Combating the Financing of Terrorism
EDD Enhanced Due Diligence
FRA Financial Reporting Autority
FSP Financial Services Provider
PEP Politically Exposed Persons
KYC Know Your Customer
RFB Relevant Financial Business
SAR Sospicious Activity Reports
The internal control system and risk management
The internal control system consists of a set of rules, procedures, and organizational structures designed to ensure the effectiveness and efficiency of business processes, the protection of the value of company assets and the sound management of assets held on behalf of clients, the reliability and integrity of accounting and management information, and compliance with applicable regulations. YOURADN is committed to implementing a comprehensive and efficient internal control system, taking into account the various applicable regulations and the various areas of activity. The control system is structured across multiple levels, each with its own specific responsibilities. Specifically, in addition to the tasks institutionally assigned to the supervisory and control bodies, the following are envisaged:
– Line controls: carried out directly by those who implement a specific activity and by those responsible for supervising it;
– Risk or second-level controls: entrusted to structures other than the operational ones;
– Internal audit activities or third-level controls: delegated to the internal auditing structure.
– Credit Risk: understood as the risk of incurring losses as a result of a deterioration in the creditworthiness, leading to default, of both retail/corporate customers and institutional counterparties to which YOURADN acts as a creditor in its investment activities, as a result of which the debtor may fail to fulfill its contractual obligations in whole or in part.
– Market Risk: defined as the risk of suffering losses, even significant ones, linked to the unfavorable performance of market variables sensitive to YOURADN’s investment activities, such as interest rates, exchange rates, stock prices, volatility, and bond spreads.
– Liquidity risk: This generally manifests itself in the form of restrictions on the divestment of assets. More specifically, it is the risk that the financial instrument cannot be bought or sold without a significant reduction/increase in price due to the potential inability of the market to partially or completely accommodate the transaction.
BUSINESS RISK ASSESSMENT
Business activity, whether financial or non-financial, is always characterized by a certain degree of risk, arising from the uncertainty surrounding the achievement of corporate objectives and therefore connected to the variability of the company’s future economic value.
Since risk is inherent to a company’s business, it is essential to establish a Risk Management system within the company to ensure the control and governance of corporate risk. The primary purpose of the Risk Management function is to enable the company to derive lasting benefits from every activity it undertakes, thus contributing to the creation of value for the company and its stakeholders.
The purpose of the business risk assessment is to:
- Identify the main risks faced by the Company in its daily operations, whether financial or customer management (AML-KYC-KYB);
- Assess the likelihood of each risk impacting the Company;
- Evaluate the procedures and controls in place to mitigate these risks.
From an AML perspective, the primary risk for the Company is the initiation of a business relationship (through the sale or purchase of other cryptocurrencies and cryptographic tokens or otherwise) that leads the Company to become involved in or associated with financial crimes or terrorist activities. The potential negative impact of this risk is significant, both financially and operationally, and could result in reputational damage, loss of customers, regulatory action and fines, and lengthy legal proceedings.
There are many ways in which the Company could be involved in or associated with a financial crime, including but not limited to:
- Receiving payments from the proceeds of crime in the form of fiat currency or other cryptocurrencies;
- Providing services to known criminals, terrorists, or individuals with suspicious business activities;
- Allow sanctioned individuals or companies to circumvent asset freezes or other sanctions by allowing the transfer of funds through the Company’s platform;
- The purchase of cryptocurrencies and other cryptographic tokens which are then essentially associated with the proceeds of crime;
- Failure to identify suspicious transactions;
- Assistance in the circulation of criminal proceeds.
The Company’s compliance program includes an assessment and documentation of the risks associated with money laundering, terrorist financing, and proliferation financing within its business, enabling the Company to focus its resources where they are most needed to manage risks within its acceptance level.
1.1 EVALUATION
In carrying out a risk assessment of its business, the Company took into account the elements illustrated in the Guidelines for Virtual Asset Service Providers.
A risk-based approach allows us to identify potential risks and direct resources and efforts where the risk is greatest, while reducing requirements where the risk is low. The Company’s risk assessment captures the following factors:
- The Company’s customers, Token holders and commercial relationships of purchase, sale, exchange, crypto to crypto, fiat to crypto, crypto to fiat;
- These include risks associated with the types of customers who enter into a business relationship with the Company. Examples of customer categories that may indicate a higher risk include politically exposed persons (PEPs), sanctioned individuals or companies, customers whose nature, structure, or relationships make it difficult to identify the ultimate beneficial owner of significant or controlling interests, as well as customers who conduct transactions under unusual circumstances.
- There is a risk that sanctioned individuals and companies may attempt to use tokens as a means to circumvent currently applicable asset freezing sanctions. The Company will ensure that all token holders or users of the platform developed by the Company are checked against the relevant lists of sanctioned individuals and companies to combat such abuse.
- Token holders may, in fact, be delegated by sanctioned individuals and companies and may de facto hold them on behalf of persons prohibited from doing so. 2. The Company’s products and services and the delivery channels through which it offers them;
- These include risks associated with the types of products and services offered by the Company (i.e., tokens, wallet exchanges, interconnection between DE.Fi platforms) and the way in which such products and services are provided to customers.
- Tokens listed or undergoing ICO, or requests for exchange and trading on the Company’s platform, could be used as a means to finance terrorism or otherwise finance sanctioned individuals, companies, or groups.
3. The geographic locations in which the Company conducts its business and the geographic locations of its customers; 4. The Company’s acceptance of other cryptographic tokens or cryptocurrencies as a means of payment for tokens; 5. The Company’s purchase of cryptographic tokens and cryptocurrencies as Company assets; 6. Any other relevant factors relating to the Company’s business, its customers, and its business relationships with them.
1.2 CONTROL MEASURES
Risk management and mitigation will involve:
- Application of customer due diligence (KYC-KYB) measures to verify the identity of customers and any beneficial owners who use YOURADN services.
- Obtain additional information or conduct enhanced due diligence on higher-risk clients through specialized platforms such as the 4stop platform or other similar platforms and directly from the Company.
- Additionally, the company uses IT systems such as https://www.lseg.com/en/risk-intelligence, onfido, https://btrace.amlcrypto.io/account, and other similar platforms to manage customer data verification at various levels.
- Using official national and international services and databases to screen all customers and transactions to ensure they are not Politically Exposed Persons or subject to sanctions.
- Screening of token holders at the time of redemption/exchange to combat potential money laundering, including identifying and reporting any suspicious transactions and monitoring and controlling donations to non-governmental organizations.
- Robust record-keeping procedures.
- The company uses a computer system to identify the user of the YOURADN wallet, manage the tokens it contains, and track incoming tokens by identifying their origin.
Each potential customer will be assessed using a risk-based approach to ensure that appropriate and necessary steps are taken to obtain sufficient information about the customer’s identity and business activities.
With regard to the risk of money laundering or terrorist financing, the Company operates in a very “LOW” risk environment.
Note: In 99% of cases, clients who register on the platform or via the app are identified in person through visits from Financial Advisors authorized to provide independent advice and supervised by the local authorities in the various countries where YOURADN operates. Therefore, client identification occurs primarily in person, in addition to internal processes that include a call from our customer service team to first-time clients.
However, through the implementation of anti-money laundering (“AML”) and counter-terrorist financing (“CFT”) and proliferation procedures, the Company adopts and implements activities to mitigate the identified risks.
The Company periodically reviews this business risk assessment to ensure it remains appropriate for the services it provides.
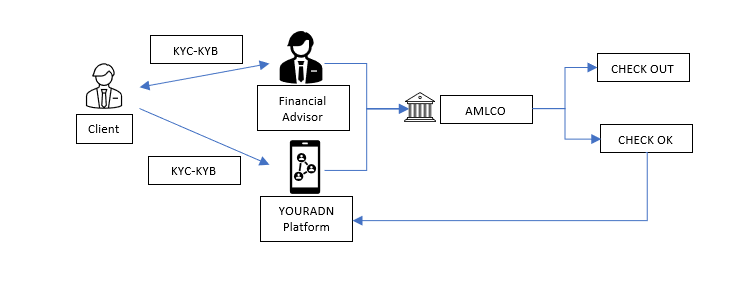
1.2.2 Procedures related to Financial Advisors for the identification of clients
YOURADN has decided to identify and monitor customers accessing the exchange platform, using appropriately trained and specialized personnel, and regularly registered in the registries kept by the various local authorities where YOURADN operates.
To qualify as a Financial Advisor, the professional must be identified and certified by submitting a copy of their high school diploma, a certificate of pending charges no older than three months from the date of inclusion in the YOURADN structure, a criminal record no older than three months, and proof of residence, if the individual is a natural person. For legal entities, a copy of the bylaws and articles of association, along with the same documents for directors and shareholders with a stake exceeding 5%.
The Financial Advisor, who passes the selection process, is included in the YOURADN structure, and must complete the training process that enables identification before starting to practice crypto asset consultancy.
1.2.3 KYC and KYB and AML procedures managed by YOURADN Financial Advisors
YOURADN’s Financial Advisor uses a physical or digital document provided by the office, which allows them to retrieve the necessary information for client profiling.
The data collection document includes the management of the collection of identity documents, proof of residence, and any other document certifying the origin of the funds (in the case of purchasing cryptocurrencies or tokens), or the origin of the cryptocurrencies or tokens in the case of custody or deposit in the wallet at YOURADN.
This documentation is sent to the CS department, which activates the wallet opening procedure, with the assistance of the compliance department to verify the customer’s data.
At the same time, once the customer has obtained the platform’s login credentials, they will have to complete the online procedure, which involves uploading part of their identity documentation, a selfie of them with their documents in hand, and entering proof of residence.
The identification procedure by the Financial Advisor, combined with the digital data collection procedure during the identification and wallet opening process, are monitored by the CDD which, in collaboration with the compliance department (AMLCO), determines whether or not the opening and activation of the wallet are validated.
This direction taken by YOURADN makes the overall risk LOW.
1.3 RISK-BASED APPROACH
It is important that the Company’s officers and staff, including Financial Advisors, adopt and implement the policies contained in this manual.
A risk-based approach is one of the most effective ways to protect yourself from money laundering. It’s essential to understand that certain risks associated with various elements of a customer’s profile can be indicative of potential criminal activity, such as geographic and jurisdictional factors, types of business and products, distribution channels, and prevalent transaction types and amounts.
Clients will be screened, assessed, and assigned an appropriate level of money laundering risk. Clients will be designated as high, medium, or low risk.
- The high-risk client will be subject to enhanced levels of due diligence that go beyond the core policies and principles contained in this manual;
- Medium-risk customers will be subject to the core policies and procedures contained in this manual;
- Low-risk clients may be subject to some flexibility within the policies and procedures contained in this manual, however, great care must be taken to ensure that the Company continues to meet its legal obligations.
While it is accepted that failure to submit satisfactory due diligence documentation may be indicative of a money laundering problem, it is also recognized that, due to the geographical diversity of financial activities, it may sometimes prove difficult or impossible to obtain documentation that precisely meets the criteria set out in this manual.
If this situation occurs and there is no reason to suspect money laundering, the client documentation must be forwarded to senior management and/or the Anti-Money Laundering Compliance Officer (AMLCO), along with an explanation of the issues that have arisen. Senior management, in consultation with the AMLCO, will review the documentation and consider the risks associated with accepting identification evidence that does not fall within these procedures, subsequently providing staff with advice and guidance as appropriate. The risks considered in the assessment and decision-making process and the conclusions reached should be adequately documented for the client’s KYC file, with appropriate approval from those involved. Only senior management, in consultation with the AMLCO or MLRO, can determine the high risk level to be assigned to a particular client or approve documentation that does not meet the exact requirements of the Company’s AML policy.
All clients are subject to a risk assessment so that the likely levels of future monitoring are anticipated and reasonable. Risk assessments will be recorded in the file. Due diligence requirements and planned future monitoring must be commensurate with the level of risk associated with the client, and enhanced due diligence will be required for all higher-risk clients.
1.4 DATABASE SCREENING
The Company uses a highly structured intelligence database (via external platforms and linked to due diligence processes) containing the names of known criminals such as money launderers, terrorists, fraudsters, individuals on government blacklists, etc., along with country profiles of jurisdictions known for high levels of criminal activity. These databases also contain the names of Politically Exposed Persons (PEPs), for which further details can be found in the following sections of this manual.
The Company screens each new client (all relevant persons) against a recognized database as part of the identification process upon receipt of a request for services and periodically thereafter. Through this database, all clients will be screened against applicable sanctions lists to ensure that their business is not conducted with countries subject to sanctions imposed by the EU (European Union), the UN (United Nations), or OFAC (Office of Foreign Assets Control), which includes the Specially Designated Nationals (SDN) list and the Blocked Persons list.
Further action required will depend on the screening results. However, senior management and/or AMLCO must be informed of any database findings that warrant consideration for designating the client as high-risk.
1.5 HIGH-RISK CUSTOMERS
A high-risk customer is one that poses a higher-than-normal adverse risk of involvement in money laundering or raises concerns regarding money laundering requirements or any other issue that senior management or AMLCO considers significant.
To mitigate the risks associated with high-risk clients, it will be necessary to consider applying enhanced due diligence to such clients in terms of initial approval and ongoing monitoring. Senior management, in consultation with AMLCO, will determine whether the level of risk is acceptable.
Enhanced due diligence (“EDD”) should go beyond the standard requirements for client approval and monitoring, as contained in this manual. Because the reasons for high-risk designation vary from client to client, the nature and level of improvement should be determined separately as high-risk clients are identified, and procedures should explain how to minimize increased risks.
If it is determined that a client meeting the criteria for high-risk designation does not warrant enhanced due diligence, the reasons for the decision and how the risks are mitigated should still be fully documented and included in the client’s file.
Furthermore, all EDD procedures performed during the approval process, along with the proposed procedures for future monitoring, should be fully documented and incorporated into the client’s file. In the event that future issues arise where staff may not readily recall the steps taken, the Company will be able to provide evidence of the due diligence performed at the time and provide the rationale for the proposed ongoing monitoring.
International best practices recommend paying particular attention to the following issues:
- High-risk countries;
- Politically Exposed Persons (“PEPs”);
- Attractive or money laundering businesses.
All high-risk relationships will be recorded for reporting and monitoring purposes.
1.6 HIGH-RISK AND NON-COMPLIANT COUNTRIES
Some countries are associated with predicate money laundering crimes such as drug trafficking, fraud, and corruption and, as a result, pose a greater potential risk to the Company. Doing business with individuals from such countries may expose the Company to greater reputational and legal risks.
Particular attention should be given to countries:
- without effective or equivalent anti-money laundering strategies;
- where cash is the prevailing and normal medium of exchange;
- political instability and/or high levels of corruption in the public or private sector;
- known countries of transit or drug trafficking.
The Company will consult publicly available databases or any lists published by the FIU, the OAM, the CNMV, and the individual central banks of the countries in which the company operates and determine whether clients’ connections to the listed countries justify a high-risk rating. Consideration should be given to how prevailing risks can be mitigated by conducting additional and more detailed due diligence. Caution should be exercised when accepting identification documents, especially certified copies, from high-risk or non-compliant countries.
1.7 POLITICALLY EXPOSED PERSONS (“PEPs”)
A politically exposed person, or PEP, is a term used to describe a person holding a public position who may be vulnerable to corruption. The following list contains examples of people who may be considered PEPs, although this list is not intended to be exhaustive:
- Head of State;
- Ministers and government politicians;
- Influential public officials;
- Judges;
- Military commanders and senior military officers;
- Family members or close associates of any of the above;
- Business partners or business connections of any of the above.
A negative risk is created for PEPs as they may use their public position, or find that their public position is being unknowingly used, for their own personal benefit or for the benefit of others who may be involved in illegal activities such as corruption, bribery and fraud.
PEPs pose significant reputational risk to a financial services provider if it is discovered that the institution is involved with a public official abusing his position. The adverse risk increases significantly when a PEP is located in a high-risk country.
The Company will ensure that each beneficial owner or underlying data controller is not a PEP by performing searches on official national and international databases to screen names against its own database or by referencing publicly available information. The results of this check will be recorded. If a PEP is identified, the Company:
- Assign the customer a high risk rating;
- Complete the PEP Report, ensuring that Senior Management and the Board of Directors approve the establishment of a business with the client;
- Conduct enhanced due diligence and be vigilant in monitoring the business relationship;
- Ensure that reasonable steps will be taken to establish the source of wealth and source of funds;
- PEP relationships will be tracked in View Point for reporting and monitoring purposes.
1.8 INDIVIDUALS AND ENTITIES SANCTIONED
When considering accepting new clients, care must be taken to ensure that the Company does not conduct business in countries affected by sanctions imposed by the EU (European Union), UN (United Nations), or OFAC (Office of Foreign Assets Control) as a result of accepting that new business.
Pursuant to the Proceeds of Crime Act, the Anti-Money Laundering Act, and the Terrorism Act, the Company is required to report suspicious activity to the Corporate Accounting Authority if it discovers a relationship that violates a sanctioning measure or a provision of the Law.
The Company must document and record all actions taken to comply with the sanctions regime and the rationale for such action. Senior management, in consultation with AMCLO, will assess whether further action is necessary, such as freezing funds and/or informing the authorities as required by relevant laws.
All individuals/entities identified in the sanctions list, if any, will be registered for reporting and monitoring purposes.
Strengthened Due Diligence
- Obtain additional customer information, such as the customer’s reputation and background, from a wider variety of sources prior to establishing the business relationship and use the information to inform the customer’s risk profile
- Conduct further research (e.g. internet searches using independent and open sources) to better inform the client’s risk profile
- where applicable, obtain information on the intermediary’s underlying client base and its AML/CFT controls;
- If appropriate, undertake further verification procedures on the customer or beneficial owner to better understand the risk that the customer or beneficial owner may be involved in criminal activity
- Obtain additional information about the customer, such as the customer’s reputation and background, before establishing the business relationship;
- Obtain further information about the client’s source of wealth or the source of funds involved in the transaction
- Verify the source of the funds or assets involved in the transaction or business relationship to try to ensure they do not constitute the proceeds of crime
- Evaluation of the information provided regarding the destination of the funds and the reasons for the operation
- Seeking and verifying additional information from the customer on the purpose and intended nature of the transaction or business relationship
- Request that the refund payment be made through the initial account used for the investment or an account in the client’s sole or joint name
- Increase the frequency and intensity of transaction monitoring
Simplified Due Diligence
- Limitation of the extent, type or timing of CDD measures
- Obtain less customer identifying data
- Changing the type of verification performed on the customer’s identity
- Inferring the purpose and nature of the transactions or the established business relationship based on the type of transaction carried out or the established relationship, without collecting further information or taking further steps relating to understanding the nature and purpose
- Verify the identity of the customer and the beneficial owner after the business relationship is established (for example, if transaction or account values exceed a defined monetary threshold). Reduce the frequency of customer identification updates in the case of a business relationship if the securities provider implements or is required to implement a periodic review process based on a formal cycle.
- Reduce the degree and scope of ongoing monitoring and control of transactions, for example based on a reasonable monetary threshold
1.9 THE INTERNAL SYSTEM
In addition to the direct customer identification processes, handled by Financial Advisors, the Compliance department uses an external system aligned with the platform for the automatic KYC and KYB process performed directly by the user when activating the wallet.
This procedure is always required even if the client’s identification has been performed in person by an authorized Financial Advisor.
The system currently in use is onfido https://btrace.amlcrypto.io/account, https://www.lseg.com/en/risk-intelligence
In an absolutely automatic way and within a few seconds, after collecting the appropriate documentation and the facial recognition of the user, the system determines whether to give the go-ahead or to request further information.
The further verification processes are passed to a Compliance Department officer to request the necessary documentation for further investigation.
